AWS Credentials Sources
You currently have three options to provide AWS Security Credentials:
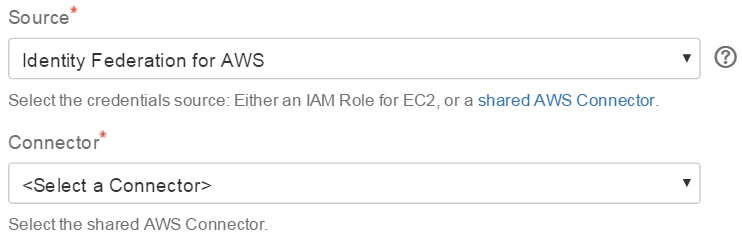
Identity Federation for AWS
| Tip |
|---|
Federated Amazon Web Services accessThis is the recommended approach to share and manage AWS credentials:
|
Refer to Administering Identity Federation for AWS for details on how to configure the connectors.
 this option requires at least one AWS Connector to be configured with System Scope to allow usage from Bamboo builds, where no user session is available
this option requires at least one AWS Connector to be configured with System Scope to allow usage from Bamboo builds, where no user session is availablea connector yields a set of temporary credentials on task execution (optionally limiting the IAM permissions)
you can configure multiple connectors to provide credentials with different IAM permissions tailored for specific use cases
 you can also facilitate Bamboo variables to ease managing connectors as outlined in How to parametrize the AWS connector via a Bamboo variable
you can also facilitate Bamboo variables to ease managing connectors as outlined in How to parametrize the AWS connector via a Bamboo variable
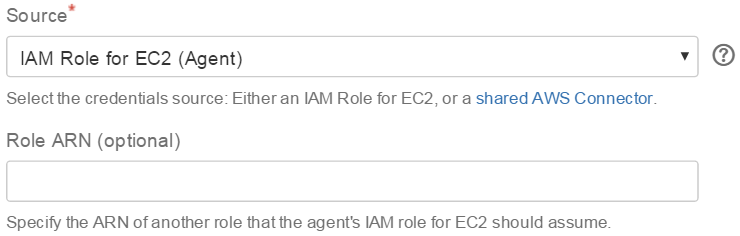
IAM Role for EC2 (Agent)
You can use IAM Roles for Amazon EC2 to optionally skip credentials configuration all together: if an agent happens to run on an EC2 instance started with an instance profile (IAM role), the tasks can be configured to facilitate those credentials. Of course, the underlying IAM role needs to have sufficient permissions for the task at hand.
This credentials source requires the agent to be running on an Amazon EC2 instance started with an instance profile, which yields three scenarios:
local agent - requires the hosting Bamboo server itself to run on EC2
remote agent - requires the remote agent to run on EC2
elastic agent - requires the elastic agent to run on EC2
 You can optionally specify the ARN of another role that the agent's IAM role for EC2 should assume via the instance profile credentials - this enables various scenarios, notably switching to roles across your own AWS accounts and third-party.AWS accounts (cross-account IAM roles).
You can optionally specify the ARN of another role that the agent's IAM role for EC2 should assume via the instance profile credentials - this enables various scenarios, notably switching to roles across your own AWS accounts and third-party.AWS accounts (cross-account IAM roles).
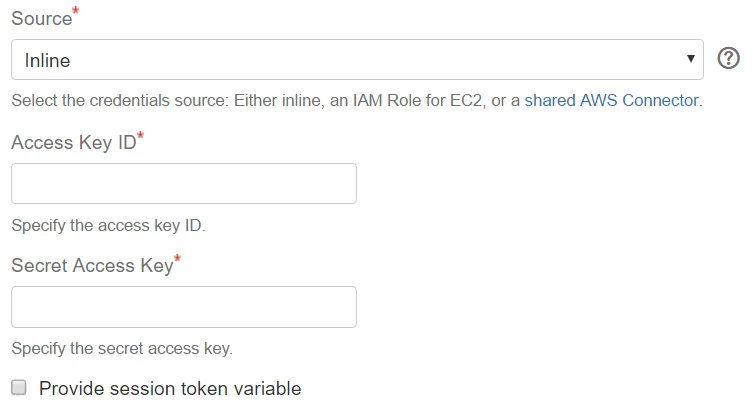
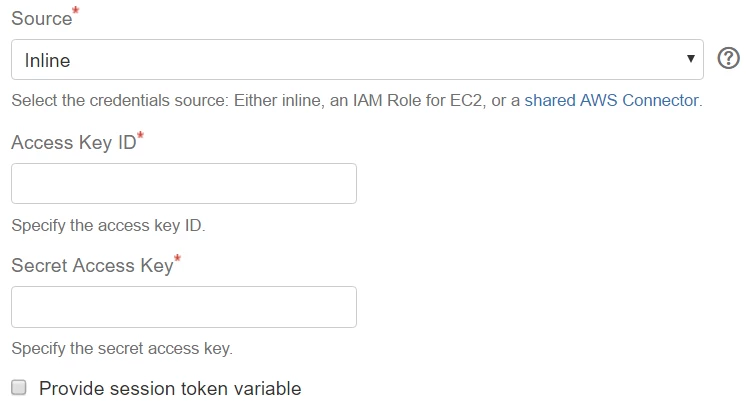
Inline
| Note |
|---|
No Real EncryptionThis is not recommended, but easy to get started with:
Please note that the Bamboo EncryptionService API naming is misleading for the time being - as properly phrased in the method summary of com.atlassian.bamboo.security.EncryptionServiceImpl, the 💡Real encryption is available by using the integration with Identity Federation for AWS (Bamboo) instead. |
| Tip |
|---|
Support for temporary credentialsAs of Tasks for AWS 2.14.1, you can also specify an optional session token via a Bamboo variable to support advanced scenarios where temporary AWS credentials can be retrieved from sources not directly supported yet (e.g SAML - refer to https://utoolity.atlassian.net/browse/UAA-267 for details):
|
If you prefer this solution, you might still want to ease credentials reuse via variable substitution as follows:
configure Access Key and Secret Key as e.g.
${bamboo.awsAccessKeyPassword}and${bamboo.awsSecretKeyPassword}define plan and/or global variables for the configured variable names (i.e.
awsAccessKeyPasswordandawsSecretKeyPasswordgiven this example) with the actual credentials, which will then be substituted on task execution accordingly
AWS China Regions
| Include Page | ||||
|---|---|---|---|---|
|
AWS GovCloud (US) Regions
| Include Page | ||||
|---|---|---|---|---|
|