Configuration
To configure an AWS Connector:
Navigate to the Identity Federation for AWS configuration.
Click Edit for an existing AWS Connector, or click Create connector to create a new one.
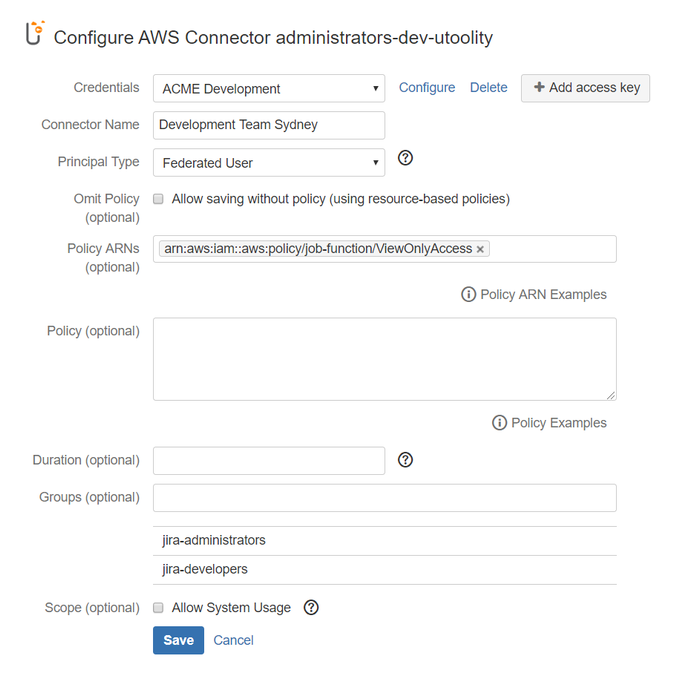
Complete the following settings:
Credentials
Select the long-term AWS security credentials to derive temporary AWS security credentials from - refer to Configuring an AWS Access Key for details.
IAM role for EC2/ECS
If you have provisioned your Atlassian workloads on Amazon EC2 (for example via the Atlassian Data Center on AWS Quick Starts), Amazon ECS, or AWS Fargate, you can enable the IAM role for EC2/ECS credentials provider to benefit from the convenience and flexibility of providing AWS security credentials via IAM roles for Amazon EC2 instances and IAM roles for Amazon ECS tasks. The resulting pseudo access key [IAM role for EC2/ECS] is added to the end of the credentials widget and can be either used directly via 'Provided' or assume another role via the ' Assumed Role' principal types.
Connector Name
Specify a custom name to identify this connector.
Principal Type
Select one of the supported principal types:
Capabilities and Restrictions
Each principal type has different capabilities and restrictions regarding credential lifetime, single sign-on (SSO) to the AWS Management Console, Multi-Factor Authentication (MFA) and calling the IAM and STS APIs in turn, see Comparing Features of AWS STS APIs for details.
| Principal Type | Explanation | Credential lifetime (min/max/default) | Learn more at AWS |
|---|---|---|---|
| Assumed Role | Yields temporary AWS security credentials for an assumed role with the Atlassian user name and an optional External ID and an optional IAM Policy (if absent, AWS applies a default) In order to use the Assumed Role principal type, you need to Grant an IAM Group Permission to Create Temporary Credentials! This example policy grants permission to access the AWS STS | 15m/12hr/1hr 1) | |
| Federated User | Yields temporary AWS security credentials for a federated user with the Atlassian user name and an optional, yet typically required IAM Policy (check Omit IAM Policy when resource-based policies are used instead) In order to use the Federated User principal type, you need to Grant an IAM Group Permission to Create Temporary Credentials! This example policy grants permission to access the AWS STS Federated User does not allow to access IAM or STS APIs, for example when creating IAM resources via CloudFormation - use Assume Role for these scenarios instead. | IAM user: 15m/36hr/12hr Root account: 15m/1hr/1hr | |
| IAM User (session token) | Yields temporary AWS security credentials for the selected IAM user (recommended) or AWS account (disadvised) itself IAM User (session token) does not allow to specify IAM policies or distinguish users - use Federated User or Assume Role for these scenarios instead. | IAM user: 15m/36hr/12hr Root account: 15m/1hr/1hr | |
| Notes | 1) The 12hr maximum is only available with an appropriately configured Maximum Session Duration Setting for a Role. | ||
Policy ARNs
(Conditional) Specify a Managed IAM Policy ARN (supported for principal types Assume Role and Federated User)
![]() Clicking on 'Policy ARN Examples' allows you to select from a few example policies to ease getting started (just click one to copy it to the policy field) - links to the IAM Policy Simulator are also provided.
Clicking on 'Policy ARN Examples' allows you to select from a few example policies to ease getting started (just click one to copy it to the policy field) - links to the IAM Policy Simulator are also provided.
Policy
(Conditional) Specify an Inline IAM Policy (supported for principal types Assume Role and Federated User)
![]() Clicking on 'Policy Examples' allows you to select from a few example policies to ease getting started (just click one to copy it to the policy field) - links to the AWS Policy Generator and the IAM Policy Simulator are also provided.
Clicking on 'Policy Examples' allows you to select from a few example policies to ease getting started (just click one to copy it to the policy field) - links to the AWS Policy Generator and the IAM Policy Simulator are also provided.
Duration
(Optional) Set the number of seconds temporary credentials based on this connector are valid - leave empty to use the AWS default credential lifetime (refer to table Principal Types above for details).
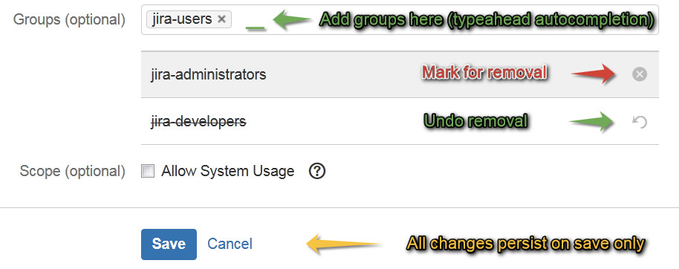
Groups
(Optional) Grant the permission to use this Connector to one or more of your Jira, Confluence, Bitbucket, or Bamboo groups:
By default, administrators always have permission to use all connectors – this can be adjusted by Disabling implicit connector visibility for administrators (experimental).
click into the selection box to search for groups
start typing to narrow down the selection
 Performance with more than 100 groups
Performance with more than 100 groupsIf there are more than 100 groups, you need to type at least one character to make all matching groups appear.
 Depending on the number of groups and naming scheme paired with browser and system performance, frequently used characters like 'e' might still yield slightly sluggish behavior - typing quickly should circumvent such sluggishness, if any!
Depending on the number of groups and naming scheme paired with browser and system performance, frequently used characters like 'e' might still yield slightly sluggish behavior - typing quickly should circumvent such sluggishness, if any!select each desired group
 all changes persist on save of the connector only
all changes persist on save of the connector only
Scope
(Optional) Select System Scope to allow usage of this AWS Connector from elevated code without an active user session (e.g. by other apps like Tasks for AWS and Automation with AWS).
How-to Articles
Filter by label
There are no items with the selected labels at this time.
Frequently Asked Questions (FAQ)
Atlassian account required